On this page, you will learn about a commonly used method of cryptography that is more secure.
The fundamental problem that cryptography is trying to solve is how to get a message to your friend that can't be intercepted by your enemies. Symmetric encryption has a fundamental weakness: the encryption key is itself a message that needs to be send to your friend but not intercepted by your enemy.
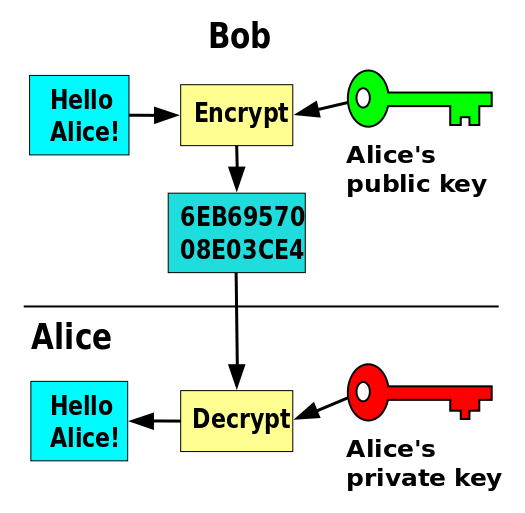
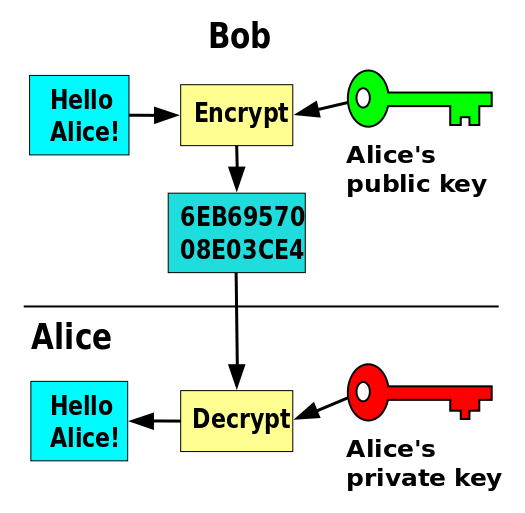
Public key cryptography is a mathematical technique to avoid the need to communicate a secret key from one person to another. Instead, each person has two keys: a private key known only to that person and a public key that everyone in the world is allowed to know. If Bob wants to send Alice a secret message, he encrypts it with Alice's public key. Then no one but Alice can decrypt it. Only her private key can undo the encryption, and no one can figure out the private key from the public key.
Secure HTTP connections (those that use https:// instead of http://) use a protocol called Transport Layer Security (TLS) or maybe an older version called Secure Sockets Layer (SSL). Both are based on public key cryptography. With SSL/TLS, the site you are visiting sends its public key, and your browser uses it to encrypt the information you send.
SSL/TLS (secure sockets layer/transport layer security) is the standard used for cryptographically secured information transfer on the Internet.
In order to work properly, a cryptographic function has to be easy for the private key holder to invert, but hard for anyone else to invert. How do we know what "hard" means? For example, current cryptographic methods rely on the difficulty of finding prime factors of very large numbers. There's no proof that someone won't come up with a fast way to do that, but people are pretty confident about it because the problem has been well studied by many mathematicians. (On the other hand, when quantum computers become practical, factorization will be easy, and new cryptographic methods will be needed.)
What makes it possible for mathematicians to study the difficulty of breaking Internet cryptography is that the method used—the cryptographic function—is openly published. This may seem strange; if you want to keep secrets, shouldn't you keep the technique secret, too? But secret algorithms can have weaknesses that go undiscovered until some bad guy exploits them. Open standards allow an algorithm to be studied before it is used in practice.
Certificate authorities issue digital certificates that verify who owns the encryption keys used for secured communications.
Public key cryptography doesn't solve all the problems, because an eavesdropper (say, Eve) might publish a fake public key pretending to be Alice. Then Bob might accidentally encrypt their message for Alice using the Eve's fake key, and then the Eve can read the message. In practice, this is partly fixed by relying on trusted third parties, called Certificate Authorities, to certify public keys. In your browser's security options you can see all of the Certificate Authorities that it trusts.